24th February 2026
24th February 2026
When Mark Curphey registered the owasp.org domain and announced the project on a security mailing list on the 9th of September 2001, there was no particular reason to expect that it would become one of the defining frameworks in the world of application security. Yet, OWASP, originally the Open Web Application Security Project, has done exactly that, growing from an informal community into a globally recognised nonprofit foundation that shapes how developers, security professionals and businesses think about the security of software. In February 2023, the board voted to update the name to the Open Worldwide Application Security Project, a change that better reflects its modern scope, which now extends beyond web applications to cover IoT, APIs and software security more broadly.
At its heart, OWASP operates on a straightforward principle: knowledge about software security should be free and openly accessible to everyone. The foundation became incorporated as a United States 501(c)(3) nonprofit charity on the 21st of April 2004, when Jeff Williams and Dave Wichers formalised the legal structure in Delaware. What began as an informal mailing list community grew into one of the most trusted independent voices in application security, underpinned by a community-driven model in which volunteers and corporate supporters alike contribute to a shared vision.
The OWASP Top 10
Of all OWASP's contributions, the OWASP Top 10 remains its most widely cited publication. First released in 2003, it is a standard awareness document representing broad consensus among security experts about the most critical risks facing web applications. The list is updated periodically, with a 2025 edition now published, following the 2021 edition.
The 2021 edition reorganised a number of longstanding categories to reflect how the threat landscape has shifted. Broken access control rose to the top position, reflecting its presence in 94 per cent of tested applications, while injection (which encompasses SQL injection and cross-site scripting, among others) fell to third place. Cryptographic failures, previously listed as sensitive data exposure, took second place. By organising risks into categories rather than exhaustive lists of individual vulnerabilities, the Top 10 provides a practical starting point for prioritising security efforts, and it is widely referenced in compliance frameworks and security policies as a baseline. It is, however, designed to be the beginning of a conversation about security rather than the final word.
Projects and Tools
Beyond the Top 10, OWASP maintains a substantial portfolio of open-source projects spanning tools, documentation and standards. Among the most widely used is OWASP ZAP (Zed Attack Proxy), a dynamic application security testing tool that helps developers and security professionals identify vulnerabilities in web applications. Originally created in 2010 by Simon Bennetts, ZAP operates as a proxy between a tester's browser and the target application, allowing it to intercept, inspect and manipulate HTTP traffic. It supports both passive scanning, which observes traffic without modifying it, and active scanning, which simulates real attacks against targets for which the tester has explicit authorisation.
The OWASP Testing Guide is another widely consulted resource, offering a comprehensive methodology for penetration testing web applications. The OWASP API Security Project addresses the distinct risks that face APIs, which have become an increasingly prominent attack surface, and OWASP also maintains a curated directory of API security tools for those working in this area. For teams managing web application firewalls, the OWASP ModSecurity Core Rule Set provides guidance on handling false positives, which is one of the more practically demanding aspects of deploying rule-based defences. OWASP SEDATED, a more specialised project, focuses on preventing sensitive data from being committed to source code repositories, addressing a problem that continues to affect development teams of all sizes. Projects are categorised by their maturity and quality, allowing users to distinguish between stable, production-ready tools and those that are still in active development, and this tiered approach helps organisations make informed decisions about which tools are appropriate for their needs.
Influence on Industry Practice
The reach of OWASP's guidance is considerable. Security teams use its materials to structure risk assessments and threat modelling exercises, while developers integrate its recommendations into code reviews and secure coding training. Auditors and regulators frequently reference OWASP standards during compliance checks, creating a shared vocabulary that helps bridge the gap between technical staff and leadership. This alignment has done much to normalise application security as a core part of the software development lifecycle, rather than a task bolted on after the fact.
OWASP's influence also extends into regulatory and standards environments. Frameworks such as PCI DSS reference the Top 10 as part of their requirements for web application security, lending it a degree of formal weight that few community-produced documents achieve. That said, OWASP is not a regulatory body and has no enforcement powers of its own.
Education and Community
Education remains a central part of OWASP's mission. The foundation runs hundreds of local chapters across the globe, providing forums for knowledge exchange at a local level, as well as global conferences such as Global AppSec that bring together practitioners from across the industry. All of OWASP's projects, tools, documentation and chapter activities are free and open to anyone with an interest in improving application security. This open model lowers barriers for those starting out in the field and fosters collaboration across academia, industry and open-source communities, creating an environment where expertise circulates freely and innovation is encouraged.
Limitations and Appropriate Use
OWASP is not without its limitations, and it is worth acknowledging these clearly. Because it is not a regulatory body, it cannot enforce compliance, and the quality of individual projects can vary considerably. The Top 10, in particular, is sometimes misread as a comprehensive checklist that, once ticked off, certifies an application as secure. It is not. It is an awareness document designed to highlight the most prevalent categories of risk, not to enumerate every possible vulnerability. Treating it as a complete audit framework rather than a starting point for more in-depth analysis is one of the most common mistakes organisations make when engaging with OWASP materials.
The OWASP Top 10 for Large Language Model Applications
As artificial intelligence has moved from research curiosity to production deployment at scale, OWASP has responded with a dedicated framework for the security risks unique to large language models. The OWASP Top 10 for Large Language Model Applications, maintained under the broader OWASP GenAI Security Project, was first published in 2023 as a community-driven effort to document vulnerabilities specific to LLM-powered applications. A 2025 edition has since been released, reflecting how quickly both the technology and the associated threat landscape have evolved.
The list shares the same philosophy as the web application Top 10, using categories to frame risk rather than enumerating every individual attack variant. Its 2025 edition identifies prompt injection as the leading concern, a class of vulnerability in which crafted inputs cause a model to behave in unintended ways, whether by ignoring instructions, leaking sensitive information or performing unauthorised actions. Other entries cover sensitive information disclosure, supply chain risks (including vulnerable or malicious components sourced from model repositories), data and model poisoning, improper output handling, excessive agency (where an LLM is granted more autonomy or permissions than its task requires) and unbounded consumption, which addresses the risk of uncontrolled resource usage leading to service disruption or unexpected cost. Two categories introduced in the 2025 edition, system prompt leakage and vector and embedding weaknesses, reflect lessons learned from real-world RAG deployments, where retrieval-augmented pipelines have introduced new attack surfaces that did not exist in earlier LLM architectures.
The LLM Top 10 is distinct from the web application Top 10 in an important respect: because the threat landscape for AI applications is evolving considerably faster than that of traditional web software, the list is updated more frequently and carries a higher degree of uncertainty about what constitutes best practice. It is best treated as a living reference rather than a settled standard, and organisations deploying LLM-powered applications would do well to monitor the GenAI Security Project's ongoing work on agentic AI security, which addresses the additional risks that arise when models are given the ability to take real-world actions autonomously.
An Ongoing Work
In an era defined by rapid technological change and an ever-expanding threat landscape, OWASP continues to occupy a distinctive and valuable position in the world of application security. Its freely available standards, practical tools and community-driven approach have made it an indispensable reference point for organisations and individuals working to build safer software. The foundation's work is a practical demonstration that security need not be a competitive advantage hoarded by a few, but a collective responsibility shared across the entire industry.
For developers, security engineers and organisations navigating the challenges of modern software development, OWASP represents both a toolkit and a philosophy: that improving the security of software is work best done together, openly and without barriers.
 27th November 2025
27th November 2025
This time last year, I was a regular user of Perplexity. Unfortunately, it began to live to its name when news items began to appear on its previously clean home page. When ChatGPT and Anthropic Claude gained the ability to search the web one after another, there was little need to use Perplexity any longer. Before that happened, I began to use uBlock Origin to block the offending panels that I found so intrusive.
However, I still retain an enduring intolerance of intrusions into clean interfaces on public GenAI tools. Thus, when ChatGPT started to offer inspiration for using it in a dropdown panel below the text box, I began to look for ways to block it. It is not as if I need ideas from others anyway; quite enough come up for me from my daily computing.
While disabling memory may help, I sought another way to turn the dropdown panel, only to find that there was none. That left uBlock Origin as my means of control. Unfortunately, OpenAI do not make it easy to block the offending insertion; Perplexity was very simple: right-click on the item and navigate to uBlock Origin > Block element... on the context menu that appears. Making the selection on the ChatGPT interface was unavailable because of how they structure things.
Ironically, I started to pursue the matter using the ChatGPT tool itself. All of this was on Firefox, so I could explore the code by right-clicking on the page and selecting Inspect from the context menu that appeared. Just viewing the source code was not an option either; obfuscation on the OpenAI end saw to that: they appear to use JavaScript to convert indecipherable symbols into code that a browser can render. There was some toing and froing before I got as far as a workable solution.
This needed me to get into the uBlock Origin Dashboard through selecting its icon on the toolbar (while I have it pinned there, you may need to click on the Extensions button in the same place as an additional step before all the steps that I describe here) and then clicking on the gears icon in the bottom right of the panel that appears. Once into the uBlock Origin interface, go to the My Filters tab and add the following code in there:
chatgpt.com##ul.divide-token-border-light.flex-col.divide-y > li.w-full
The first part (before the ## separator) is the URL, which may be chatgpt.openai.com for you. The rest selects the ideas panel while leaving the prompt text and hyperlink in place. That sufficed for me; a generic item is not as intrusive as anything built from your history or any other source of information. Naturally, the interface may change again, which might mean that I need to revisit the filter, but this works for now. We all learn as we go.
 23rd March 2025
23rd March 2025
Such is the state of the world at the moment that I ration my news intake for the sake of my mental wellbeing. That also includes the content that websites present to me. Last November, I was none too please to see Perplexity showing me something unwanted on its home page. However, there appeared to be no way to turn this off, in contrast to the default page shown in a new browser tab. Then, I decided to tolerate the intrusion, only for the practice to develop over time.
Then, I happened on uBlock Origin after finding that it will block unwanted parts of web pages. While it was a bit hit-and-miss to get things going on the Perplexity website, it did the job after some trial and error. Things can change, which means the blocking may need refinement. Even so, I can handle that. When YouTube became another place where I needed to block distractions like previews of other videos during a webinar.
Now, uBlock Origin has become the only ad blocker that and I still use with Firefox. Others like Ghostery broke websites, especially that of the UK Met Office with its cookie blocking; the Ryanair one was another casualty, and became one that fell foul of Pi-hole too. Thus, they were left after me for a single shot approach. Though some websites may complain, anything that cuts out distractions has to help productivity and emotional wellbeing.
 10th May 2009
10th May 2009
Now that the Release Candidate for Windows 7 is out, I have been giving it a whirl in a VirtualBox session and it, like the Beta that I had been trying too, feels a sold enough affair. I went for the complete installation route in place of the upgrade path. One surprise was that it bundled my old files into a single folder called Windows_old, and that my old user bits and bobs were folded in with this too. Even though there was nothing there that I wouldn't have missed, this still is a nice touch.
However, I have a spot of fixing to do after adding Kaspersky Internet Security 2009. Like the beta, mixing Windows 7 and Kaspersky seems not to be the way to a stable system. Whether this is down to the virtualisation aspect of the business is something that I don't know, but I have found that removing Kaspersky and replacing it made everything sing along together. Booting into Safe Mode and using msconfig to remove any incidences of Kaspersky being called at start up provides a partial restoration of service. Because the msiexec service isn't running, you need full mode before any software but pulling out any cause for execution of Kaspersky gets that back. While I suppose that I could go and put Windows 7 on a real machine to see if Kaspersky causes problems there, that's not a road that I really want to travel at this time.
 20th October 2007
20th October 2007
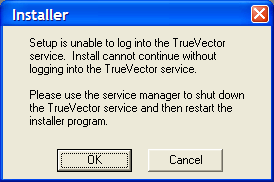
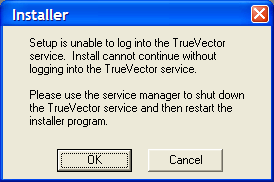
ZoneAlarm cut off VMware's access to the internet, so it was time to reinstall it. However, I messed up the reinstallation and now there seems no way to reinstate things like they were without tampering with my Windows XP installation status, and I have no intention of doing that. The thing seems to think that it can start a TrueVector service that does not exist.
Since I have to have some security software on board, I made a return to the Symantec fold with my purchase of Norton 360. That does sound extreme, but I have been curious about the software for a while now. You get the usual firewall, antivirus and antispam functions with PC tuning, anti-phishing and backup features available as well. It is supposed to be unobtrusive, so we'll see how it goes from here.
Update:
PC Pro rates the software highly, while Tech.co.uk accuses it of being bloatware. Nevertheless, the only issue that I am having with it is its insistence on having Microsoft Update turned on. For now, I am sticking with Shavlik's NetChk Protect, especially seeing what Microsoft has been doing with its update service. Have a look at Windows Secrets.com to see what I mean. Other than that, it seems to working away in the background without intruding at all.
 1st April 2007
1st April 2007
Having owned a licence of ZoneAlarm Security Suite 6, I was wondering if I would get a pop-up inviting me to upgrade, free gratis as I have a subscription, to the latest version. In the middle of my Office 2007 installation activities, the notification duly turned up to prompt me to download and install the update to version 7.
The first change you will notice is in the branding, ZoneAlarm is now owned by Check Point Software Technologies, but the real reason for my interest is my hearing that Kaspersky antivirus technology is now part of the package. In addition, learning capabilities have also been added so that you don’t get annoyed by the thing asking you if it is alright for a certain application to do something or other that seems vaguely out of order, all the time. This has been part of Norton Internet Security for a while and is certainly an asset; Windows Vista’s User Access Control feature would do well to implement some of this learning, given what I have heard of its activities. And ZoneAlarm 6 was prone to nag you a lot as well, at least it did for me.
The installation went well for me, apart from the non-activation of the antivirus functionality. This took an update and a reboot to sort out, leaving me to think that it might have emanated from the changeover to British Summer Time that took place last weekend. I shall be keeping an eye out for what happens when the changeover to Winter time takes place (don’t worry, I fully plan to enjoy the intervening time; I have more than learned to enjoy each season for its delights). Having a time changeover like this knock out your antivirus software is far from ideal. Other than that, everything is working fine, especially as the firewall is staying silent as it continues to learn.
 30th January 2007
30th January 2007
Contrary to appearances given by this blog, I am not exclusively a Windows user. In fact, I have sampled Linux on a number of occasions in the past and I use VMware to host a number of different distributions – my Ubuntu installation is updating itself as I write this – as I like to keep tabs on what is out there. I also retain a Windows 2000 installation for testing, and have had a virtual machine hosting a test release of Vista not so long ago. I also have my finger in the UNIX world with an instance of OpenSolaris, though it is currently off my system thanks to my wrecking its graphics set up. However, ZoneAlarm has been known to get ahead of itself and start blocking VMware. If you go having a look on the web, there is no solution to this beyond a complete system refresh (format the boot drive and reinstall everything again) and I must admit that this sounds like throwing out bath, baby and bathwater together. I did find another approach, though: removing ZoneAlarm and reinstalling it. This wipes all its remembered settings, including the nefarious one that conflicted with VMware in the first place. It's remarkable that no one else has considered this, but it has worked for me, and having to have the security software relearn everything again is much less painless than rebuilding your system.